Blog
Metal Blockchain Node Setup on Bare Metal: Validator Specs, Subnets, & Ops
Metal Blockchain validators are not “set it and forget it” infrastructure. They are always-on systems where a bad port rule, weak key workflow, or poor location choice can mean missed rewards, degraded uptime, or a subnet that fails its own governance rules. On Metal, the operational model is explicit enough that infrastructure design and protocol design are tightly coupled.
This article focuses on the part that matters in production: what Metal Blockchain is for, the published minimums for validator and subnet nodes, the ports that must be reachable, and the way subnet compliance rules shape hosting, access control, and auditability.
Best Servers for Web3— 1,300+ ready-to-go servers — Custom configs in 3–5 days — 21 global Tier IV & III data centers |
Metal Blockchain: Layer‑0 Design, Primary Network, and Subnets
Metal presents itself as a Layer‑0 blockchain with a primary network and custom subnets. The design lets operators run separate validator sets and workloads while scaling horizontally; Metal says a subnet can process 4,500 TPS, with aggregate throughput growing as more subnets are added.
The catch for operators is structural. Metal calls the primary network “a special subnet”, and validators on custom subnets must also validate the primary network by staking at least 2,000 METAL. So a subnet validator inherits both base-network reliability requirements and subnet-specific policy requirements.
Those policies can be strict. Metal’s subnet framework allows validators to be limited by country, KYC/AML status, or licensing. Once those rules exist, physical location, privileged-access paths, and evidence-quality logs stop being “ops nice-to-haves” and become part of subnet compliance.
Metal Blockchain Node Requirements: Compute, Storage, and Networking Ports
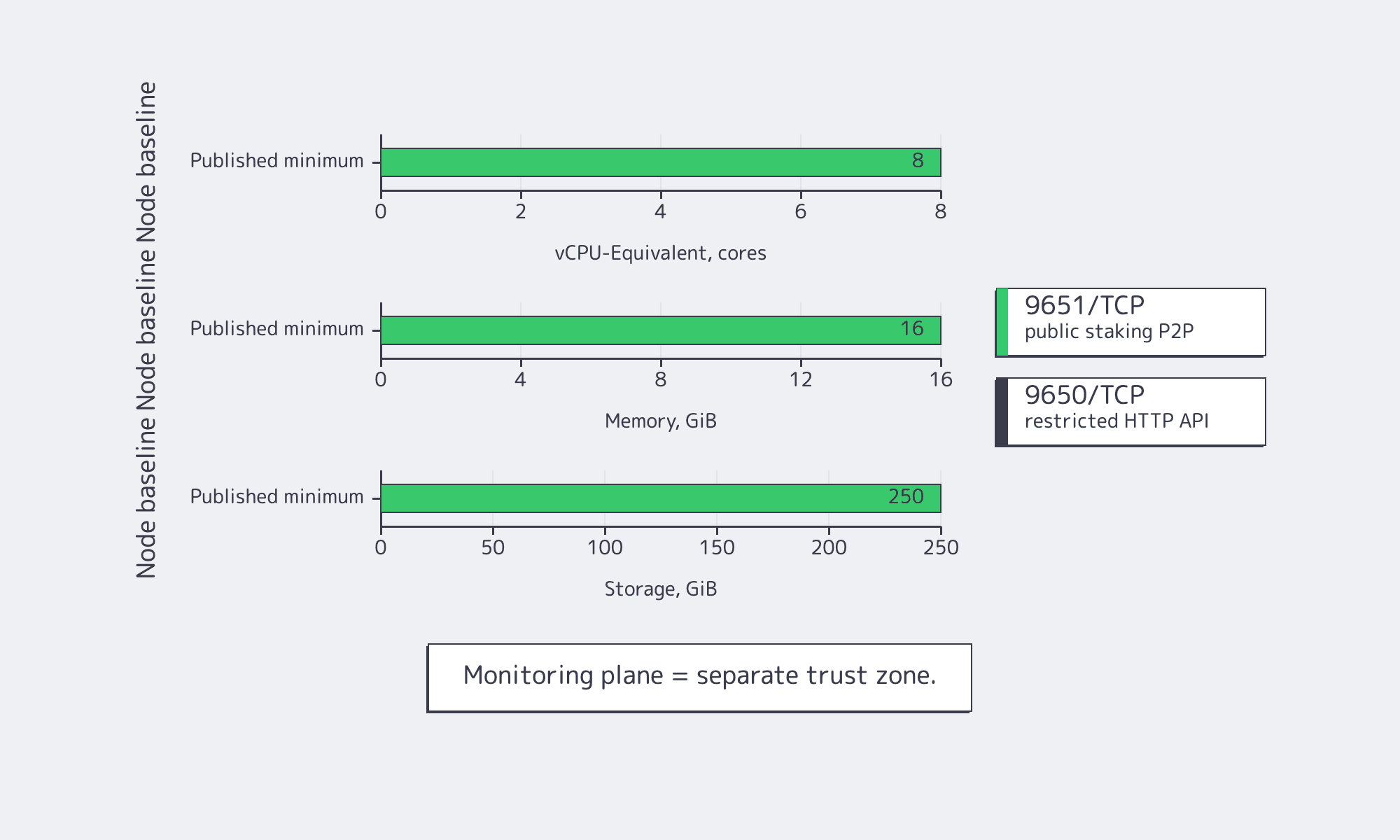
Metal’s manual deployment guide sets the baseline at 8 vCPU-equivalent, 16 GiB RAM, and 250 GiB of storage. That is enough to start; it is not always enough to stay healthy under long-lived connection growth, pruning, restores, or aggressive monitoring.
Metal Validator Node Minimum Specs vs. Production Sizing
| Node Role | Published Baseline | Ports and Exposure |
|---|---|---|
| Primary-network validator | 8 vCPU-equivalent, 16 GiB RAM, 250 GiB storage | 9651/TCP for staking P2P; 9650/TCP for HTTP API, usually restricted |
| Subnet validator | Production subnets should plan for at least five validators | Same node ports, plus any intentionally published subnet RPC paths |
| Monitoring plane | Treat as a separate trust zone | Metal warns common monitoring stacks are not hardened for public exposure |
Production sizing usually exceeds the baseline for two reasons. First, Metal’s offline pruning flow can temporarily increase disk pressure during maintenance. Second, MetalGo exposes --fd-limit because a busy node can accumulate enough peers and TCP sessions to make connection scale, not CPU, the first real failure point.
Metal Validator Node Ports and API Exposure Strategy
- 9651/TCP is the public staking port. Metal says inbound reachability is required for correct validator operation.
- 9650/TCP is the privileged HTTP API. It binds to 0.0.1 by default, which is exactly how most production teams should want it.
Metal also supports the controls that separate a working node from a defensible one: disable unused APIs, require authentication, and enable TLS. Geography matters too. An IEEE networking paper places propagation delay at roughly 5 μs/km in conventional fiber and 3.33 μs/km in near-air propagation. A subnet rule that pins validators to one jurisdiction also constrains your latency floor.
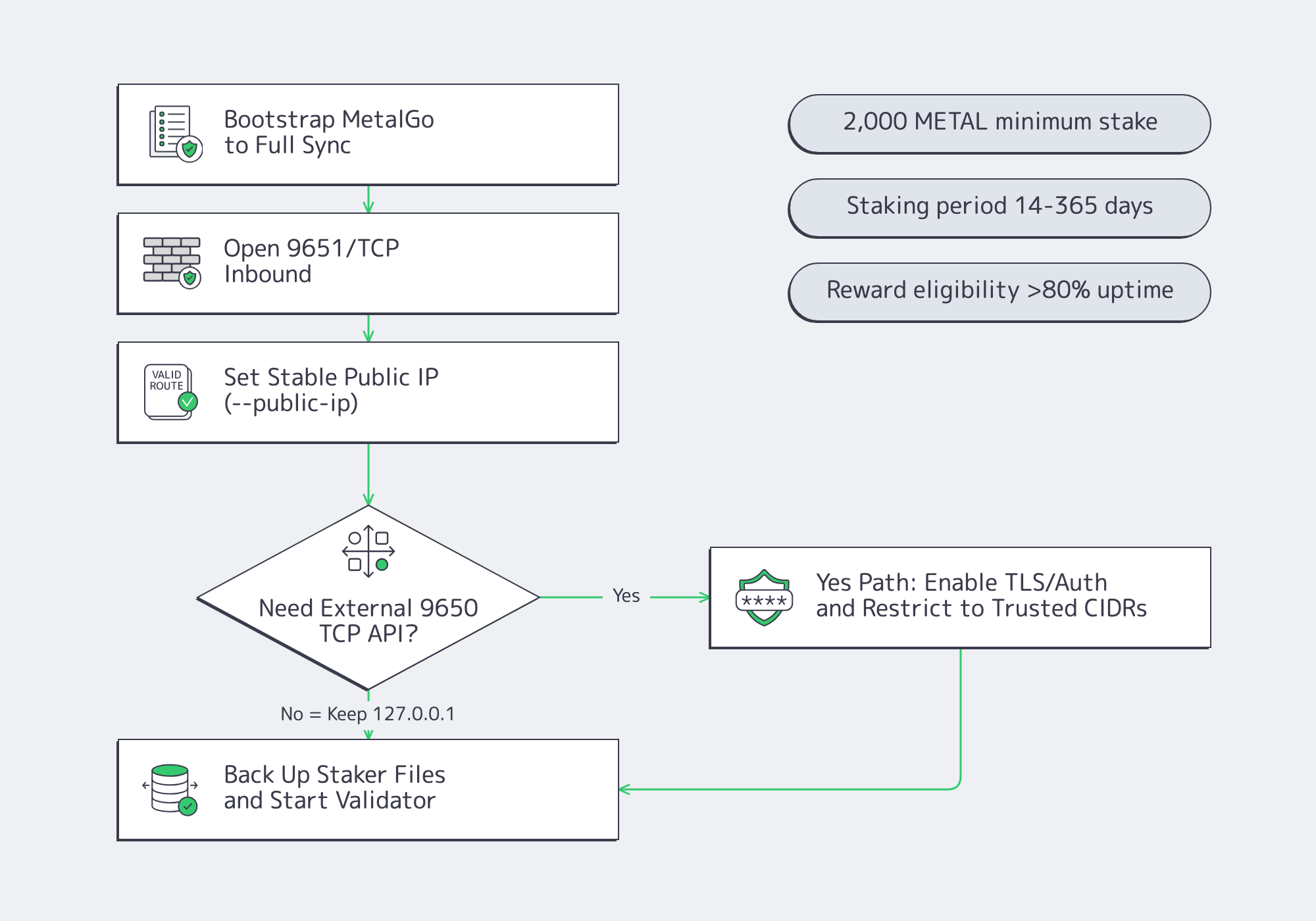
How to Run a Metal Blockchain Validator or Subnet Node on Bare Metal
A production Metal deployment starts with a fully synced node, exposes the staking path and little else, keeps the HTTP API private by default, and treats node identity, upgrades, and recovery as controlled workflows. The design goal is to separate consensus traffic, application traffic, and operator access before a failure forces that separation.
The working pattern is straightforward: bootstrap MetalGo to full sync, open inbound access for staking, set a stable public IP with --public-ip, and keep the HTTP plane limited to trusted sources if it must be reachable at all. Metal’s staking rules also make the business case for disciplined ops: validators need 2,000 METAL, a staking period of 2 weeks to 1 year, and more than 80% uptime to earn rewards. The validating host should keep only staking identity material; upgrades should always begin with staker-file backups.
What Infrastructure and Security Controls Metal Subnet Deployments Require
Metal subnet deployments need more than healthy hosts. They need launch-time governance controls, infrastructure that can satisfy location and access rules, and logs strong enough to stand up in review. In practice, keys, routing stability, privileged access, and evidence retention become part of subnet architecture, not background operations.
Governance Controls: Keys, Multisig, and “You Can’t Change It Later”
Metal’s mainnet subnet workflow requires a hardware wallet for signing, and Metal’s multisig deployment guide says multisig must be configured at deployment time and cannot be edited later. That is a blunt but useful constraint: keyholders, thresholds, and emergency procedures have to be correct before launch.
Compliance Rules: Location, Access Controls, and Evidentiary Logging
- Location and residency: a subnet can require validators in a specific country.
- Access control: privileged paths should be constrained and monitored, not exposed.
- Auditability: governance actions and infrastructure changes need evidence, not just good intentions.
Routing policy matters here too. Route leaks or hijacks can create soft outages that look like validator failure. Melbicom’s BGP Sessions support BYOIP, IPv4/IPv6, invalid-ROA rejection via RPKI, and IRR validation, which matters when endpoint stability and route auditability are part of the operating model.
Reliability Controls: Why “Five Validators” Is Only the Beginning
Metal says running a production subnet with fewer than five validators is “extremely dangerous” and “guarantees network downtime.” That is the minimum survivability number, not the resilience design.
- geographic separation, where subnet rules allow
- independent maintenance windows
- controlled upgrades
- avoidance of correlated misconfiguration
The reason to care is straightforward. In the Uptime Institute resiliency survey, more than half of respondents said their latest major outage cost > $100K, and network-related issues were the largest single cause. For validators, network architecture is a financial control.
Modern Secure Ops Pressure: Software Supply-Chain Integrity Is Now an Ops Concern
- A Federal Register notice on SBOM guidance points to more mature, machine-readable software inventory and risk workflows.
- SLSA treats provenance and build integrity as core supply-chain controls.
That lines up with NIST’s software supply-chain guidance: production node ops increasingly require proof of what binary is running, where it came from, and how it was delivered.
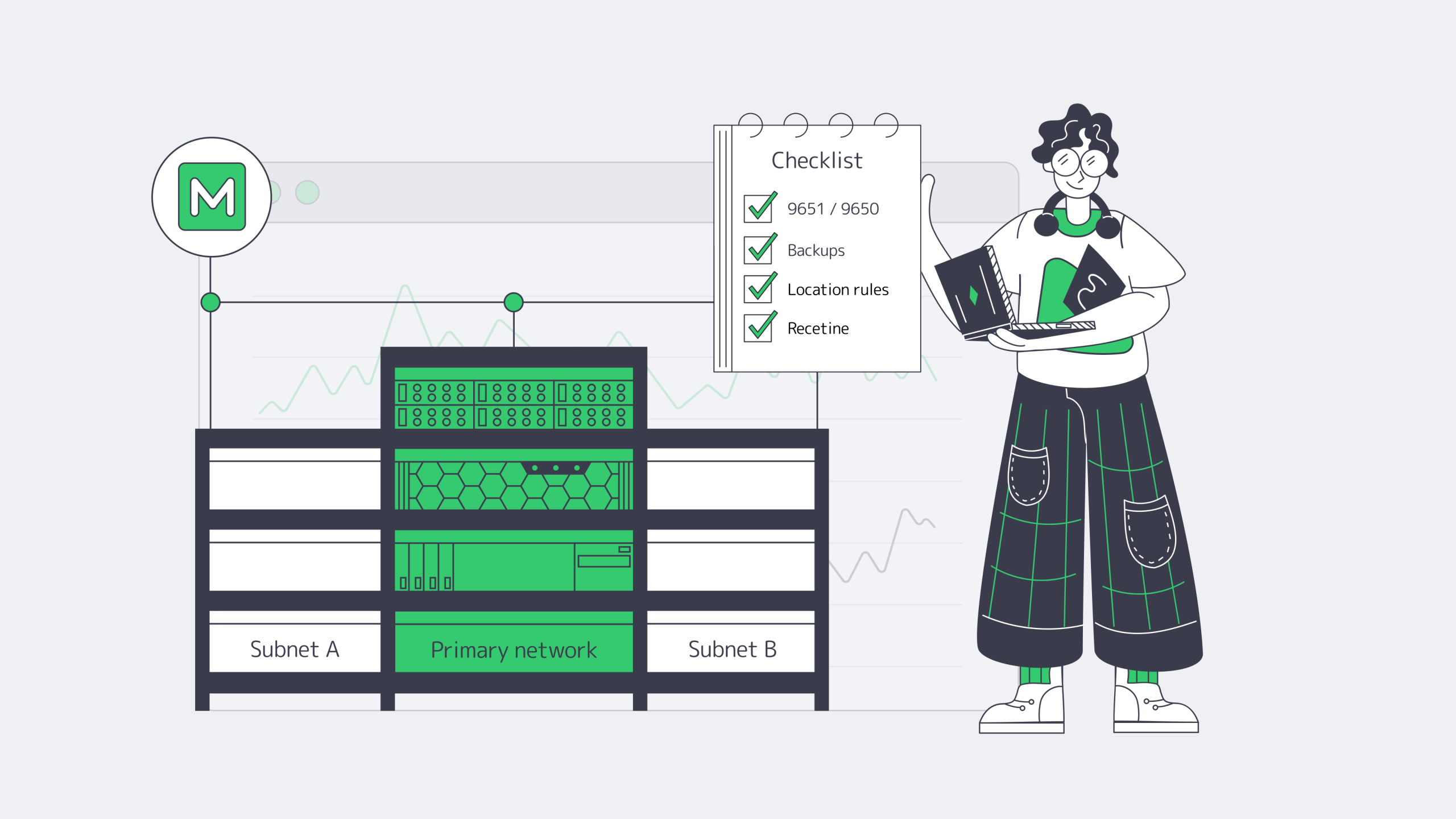
What a Production Deployment Checklist for Metal Blockchain Nodes Should Cover
A production checklist for Metal should protect the things that fail most often in the field: node identity, exposed control planes, recovery paths, upgrade discipline, and subnet governance. In practice, that means backing up staking material, keeping APIs private by default, preserving monitoring without widening exposure, and building redundancy around validator-set failure domains, not a single host.
Metal’s own docs call out the pressure points directly:
- the staker key and certificate are the node’s identity
- duplicate NodeIDs can damage uptime calculations
- monitoring stacks are not hardened for public exposure
- staker files should be backed up before upgrades
Use this cut-down deployment checklist:
- Identity and keys: back up crt, staker.key, and signer.key to 2+ secure locations.
- No duplicate identities: never run two live nodes with the same NodeID.
- Port discipline: keep exposure centered on 9651/TCP; restrict 9650/TCP to trusted sources if you open it at all.
- Public IP correctness: set
--public-ip“ - Connection and disk headroom: validate FD limits and leave spare storage for pruning and restore events.
- Monitoring and logging: keep dashboards off the public Internet and retain off-host logs for incident review.
- Patching and rollback: back up staker files before upgrades and make every version change reversible.
- Redundancy: diversify geography, routing, and maintenance windows where subnet rules allow.
- Governance security: use hardware-wallet signing and deployment-time multisig for mainnet subnets.
- Supply-chain verification: track the exact binary and provenance you are running.
Conclusion: Reliable Metal Blockchain Operations Are Designed, Not Improvised
Metal’s Layer‑0-plus-subnets model gives teams flexibility, but it also turns infrastructure into part of the control plane. Validator uptime, subnet compliance, routing policy, access design, and recovery strategy all influence whether a deployment is merely online or actually production-ready.
That is why strong Metal operations start with deliberate hosting choices: correct geography, limited control-plane exposure, auditable admin paths, off-host backups, and enough headroom to survive pruning, restores, and upgrade mistakes. The best validator environment is not the cheapest one that boots; it is the one that keeps working when the easy assumptions break.
- Treat 9650/TCP as a control plane, not a public service.
- Choose validator locations that satisfy subnet rules before optimizing for convenience.
- Size for peer churn, pruning, and restores, not only steady-state averages.
- Keep staker identity, rollback artifacts, and monitoring data recoverable off-host.
- Build redundancy across failure domains that can be explained and audited.
Dedicated Servers for Metal Validators
Deploy Metal validator and subnet nodes on bare metal with stable routing, private API exposure, and enough headroom for pruning, restores, and uptime-sensitive operations.