Blog

Fortress-Like Security for Affiliate Networks on Dedicated Servers
Affiliate marketing’s growth has drawn a parallel boom in cyber risk. The signals are clear: nearly 40% of affiliate traffic is now fraudulent, a drain on budgets and an assault on attribution accuracy. At the same time, large-scale DDoS attacks have spiked 358% year over year, routinely taking down tracking, landing pages, and API endpoints when they’re needed most. The result is revenue leakage at multiple layers—acquisition, conversion, and payout—unless the infrastructure is designed to resist modern attack patterns end-to-end.
Choose Melbicom— 1,300+ ready-to-go servers — 21 global Tier IV & III data centers — 55+ PoP CDN across 6 continents |
 |
The Attack Surface: From Fraudulent Traffic to Record DDoS Volumes
Bots and hostile automation now masquerade convincingly as human visitors, poisoning traffic quality, inflating conversions, and triggering phantom payouts. That “almost two-fifths” fraud share isn’t a rounding error; it’s the difference between profitable media buying and unprofitable campaigns that look healthy in reporting but don’t cash-flow in reality. Adversaries also target the high-value niches—adult, crypto, iGaming—where even short outages can derail revenue. On the availability side, volumetric DDoS assaults now arrive at a pace that once qualified as rare “black swan” events, with attack counts in a single quarter rivaling an entire preceding year. Affiliates that rely on instant redirects, postbacks, and real-time decisioning are uniquely exposed: if any link in the chain stalls, conversions evaporate, partners lose trust, and reputation suffers.
Historically, networks fretted over lower-grade nuisances—basic click fraud, crude scraper bots, trivial script injections. Those haven’t vanished, but they’re no longer the main story. The center of gravity has shifted to industrialized fraud operations and high-throughput denial attacks, demanding infrastructure, not just point tools, as the primary defense.
High-Performance Dedicated Servers for Affiliate Marketing: The Security Fortress
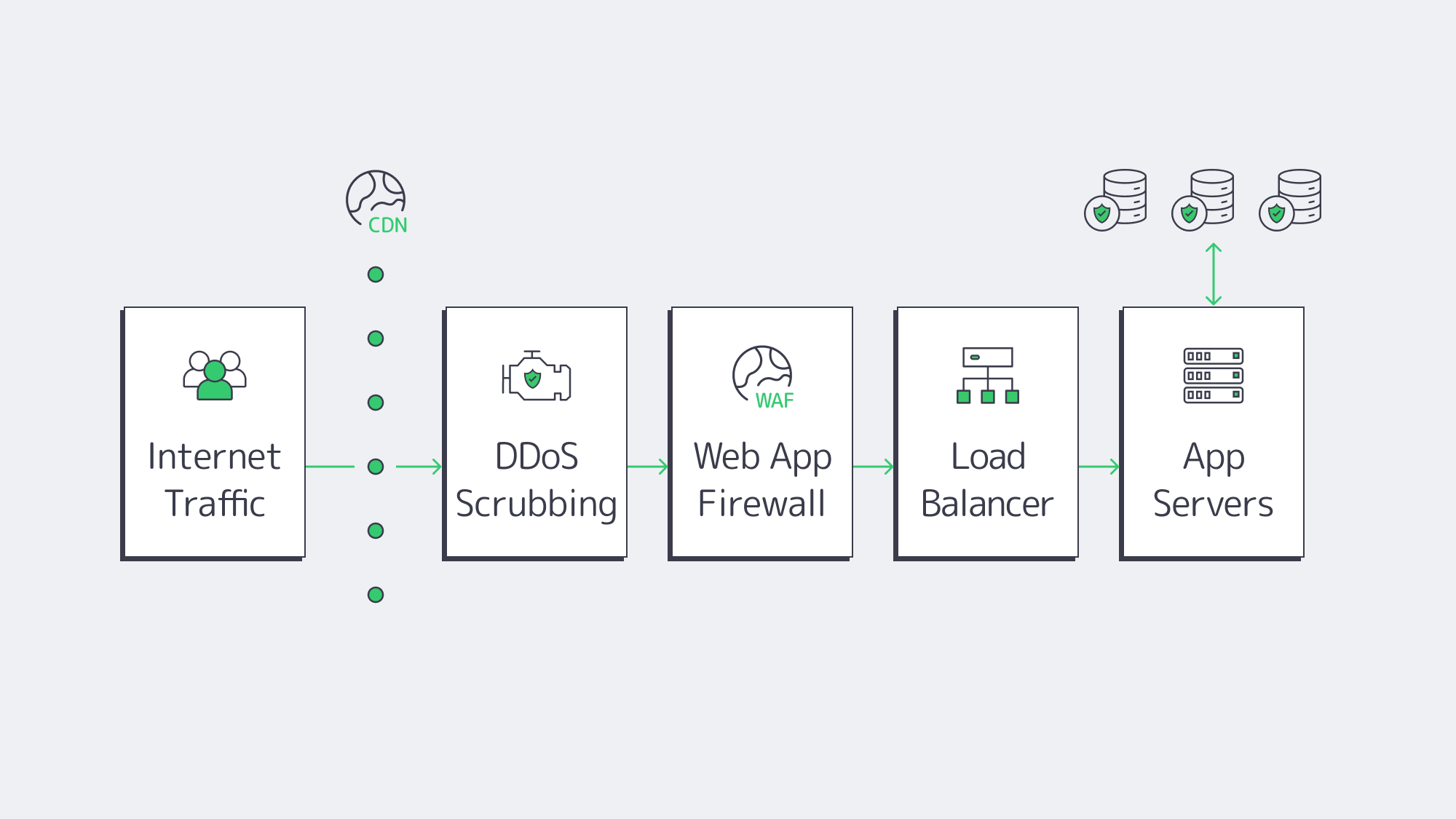
Dedicated servers provide the security posture affiliates increasingly need: isolation, transparency, and control. Single-tenant hardware means a smaller, well-defined attack surface and the freedom to set aggressive policies without worrying about noisy neighbors or cross-tenant risk. More importantly, the dedicated model lets you compose defenses in layers—network, transport, application, and data—so that no single tactic (or single failure) topples the stack.
DDoS mitigation that keeps the revenue growth
At fortress scale, protection must start upstream—before malicious floods hit your web stack. Network-level scrubbing, rate-limiting, and anomaly detection absorb volumetric surges so legitimate click-throughs, logins, and tracking calls continue to flow. In practice, that means: clean ingress pipes, consistent latency, and far fewer “brownout” conversions during hostile peaks. Attack frequency is up 358%, so always-on mitigation is now table stakes rather than an optional add-on.
For placement strategy, geographic distribution matters. Deploying nodes in multiple facilities creates air-gaps between failure domains and gives you more vantage points to shift traffic when a region is targeted. Melbicom operates 21 global data centers featuring Tier IV and Tier III halls—and per-server capacity up to 200 Gbps—enabling high-bandwidth configurations that resist and reroute hostile traffic without sacrificing user experience.
WAF and bot controls: Gatekeeping the app layer
A modern Web Application Firewall (and associated bot management) filters the subtler threats—credential stuffing against login portals, injection attempts on tracking or admin APIs, and fake sign-ups that skew CPA economics. On dedicated servers you can tune rulesets for your actual traffic patterns (e.g., known publisher IP ranges or geo allowlists), deploy deception endpoints, and enforce stricter policies without collateral damage to other tenants—because there aren’t any.
Encryption and key security: Seal the inner core
Strong TLS at the edge and encryption at rest across click logs, conversion tables, and payment records cut off a whole class of regulatory and breach risk. Dedicated environments simplify key management—HSMs, TPM-backed stores, and tight OS-level hardening—so that even if someone touches the storage, they don’t touch the data.
Multi-server redundancy: No single point of failure
Affiliate workflows are chains: source click → redirect → landing page → conversion → postback → payout. Redundancy ensures a break in one link doesn’t snap the chain. Active-active clusters and multi-region failover keep redirectors and tracking online when you’re under duress or during maintenance windows. When combined with a CDN footprint of 50+ nodes across 36 countries, static assets and cached pages stay close to users while origin traffic stays controlled and predictable.
Performance as Protection: Speed That Preserves Conversions
Security hardening must not slow the business. Properly built, fast dedicated hosting for CPA networks delivers the opposite: security and speed. Capacity at the NIC, kernel tuning for high-concurrency HTTP, and modern TLS offload keep latency low while defenses stay engaged. The payoff is tangible: fewer rage-quits on mobile, healthier quality scores, and steadier EPC when campaigns surge.
Reduce affiliate landing-page load times
Reducing time-to-first-byte and keeping render paths lean is itself a fraud- and DDoS-resilience tactic: the less time each session spends in the funnel, the less exposure to synthetic traffic stalls and cascade failures. Caching at the CDN edge plus small, fast origins minimizes origin load under attack and keeps human users moving.
NVMe dedicated servers for conversion-rate optimisation
For heavy read/write workloads—offer catalogs, stats dashboards, event streams—NVMe storage on dedicated servers cuts I/O wait to a sliver, ensuring tracking writes and analytics reads don’t contend. That throughput headroom preserves consistency under peak loads, which is when campaigns make or lose their ROI.
Emerging Defenses: AI-Driven Detection and Adaptive Controls
Static rules alone can’t keep pace with shifting bot behavior and novel L7 attacks. Affiliates are layering AI-driven threat detection on top of the fortress: models that learn publisher baselines, session dynamics, and conversion semantics, then flag or throttle anomalies in real time. Examples include: collapsing traffic from low-reputation ASNs, quarantining bursts of “too-perfect” user agents, or pausing payouts on statistically impossible conversion paths pending review. Pair that with Zero Trust inside the private network—mutual TLS for services, short-lived tokens, device posture checks for operator consoles—and lateral movement becomes much harder even if a credential leaks.
Critically, AI-assisted controls should be integrated with automated incident response: trigger a geo-shift to a clean region, rotate keys, or ratchet WAF strictness for an affected route—without waiting for a human. On dedicated servers you control the knobs, so playbooks can touch kernel parameters, BGP policies, or CDN rules instantly. The result is a system that learns and adapts as adversaries evolve.
Quick Reference: Threats to Controls
| Threat (typical symptoms) | Revenue risk | Fortress control (dedicated-friendly) |
|---|---|---|
| Volumetric DDoS (timeouts, 5xx spikes) | Lost clicks/conversions; chargebacks | Upstream scrubbing, per-region traffic steering, high-bandwidth uplinks, multi-region origins. |
| Bot fraud (fake clicks/sign-ups) | Wasted budget; polluted attribution | WAF + bot management tuned to traffic patterns; behavioral scoring; allowlists for partners. |
| Credential abuse / panel takeover | Offer hijacks; payout fraud | MFA, device binding, strict rate limits, Zero Trust service mesh; encrypted secrets storage. |
| Origin saturation (flash crowds + attack) | Slow pages; SEO penalties; EPC drop | CDN with 50+ nodes, edge caching; NVMe origins; autoscaling playbooks and request shedding. |
Where Melbicom Fits: The Infrastructure You Control, The Outcomes You Can Trust

The strategic lesson is straightforward: security and performance must be architected—not bolted on. Dedicated servers give you the isolation to run strict policies, the capacity to absorb hostile spikes, and the control to automate incident response. Deployed across multiple regions, with a WAF in front and encryption in depth, your network becomes hard to disrupt and easy to scale. That’s how you protect revenue even as adversaries escalate.
Melbicom aligns to that blueprint. Melbicom operates 21 data centers worldwide, including Tier IV and Tier III facilities, with per-server bandwidth options up to 200 Gbps for traffic-heavy platforms. A CDN with 55+ points of presence reduces global latency, and 24/7 support helps teams act quickly when conditions change. These are the ingredients to build the fortress once—and keep it modern as threats evolve.
Order Your Dedicated Server
Secure your affiliate infrastructure with high-performance dedicated servers from Melbicom.